The 6-Digit Secret: How Authenticator Apps Verify OTP They Never Store
Authenticator apps have become the backbone of modern account security. When you enable two-factor authentication (2FA), you likely rely on tools like Google Authenticator or Microsoft Authenticator. They generate a new six-digit code every few seconds to protect your logins. But how does a website know your code is correct if it never stores that specific number? The answer lies in a highly efficient system design.
The Core Concept
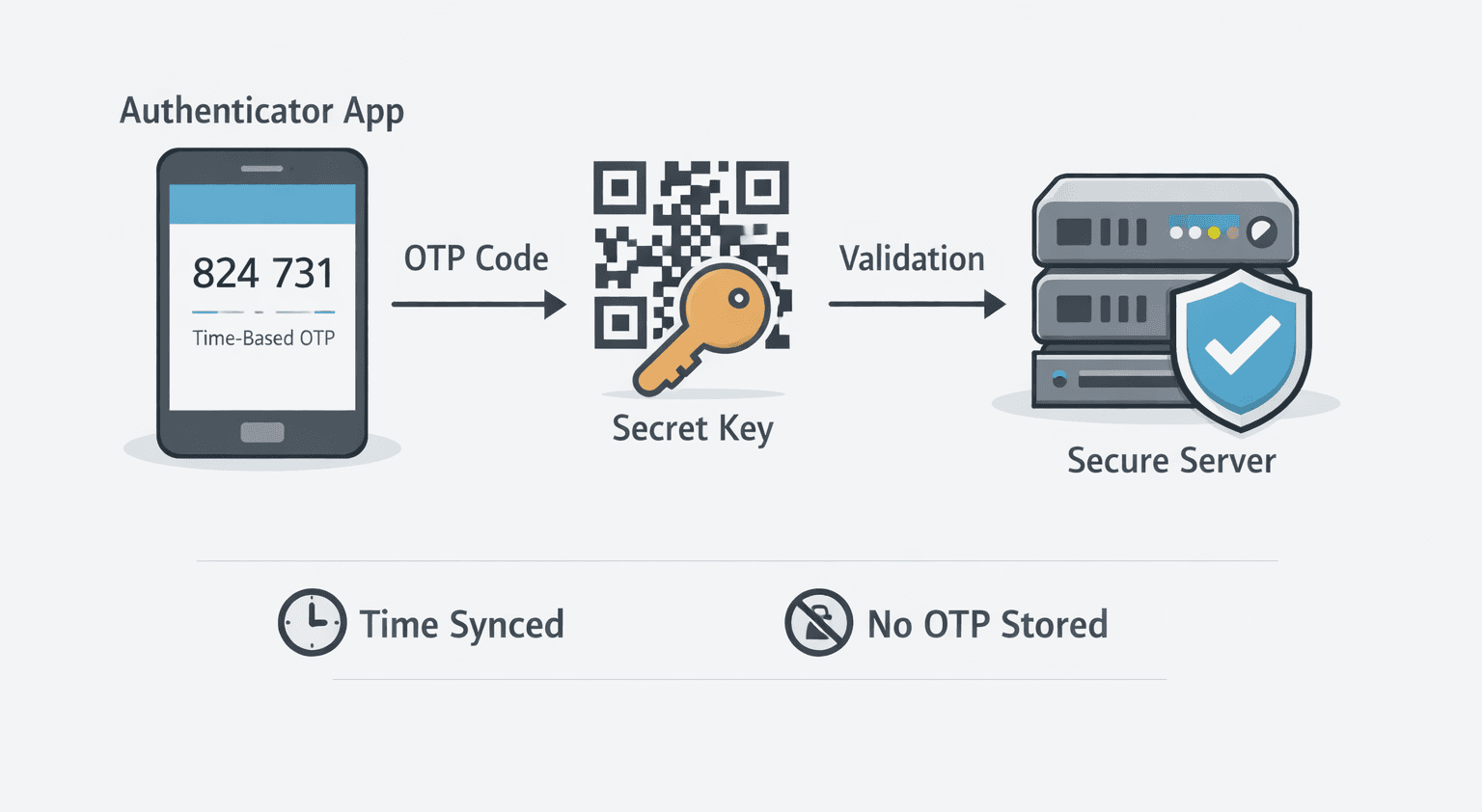
The engine driving these apps is the Time-based One-Time Password (TOTP) protocol. The most important thing to understand is that the server does not keep a database of your upcoming passwords. Instead, both your smartphone and the server independently generate the exact same code at the exact same time. They achieve this using two vital ingredients: a shared secret and the current time.
System Design in Action
The architecture of a TOTP system is built on independent calculation rather than storage. Here is how the process flows:
Secret Sharing: When you first configure 2FA, the server generates a unique, random secret key. It shares this key with your authenticator app, typically translated into a scannable QR code.
Client-Side Generation: Your app saves this secret key securely on your device. Whenever you open the app, it uses the secret and the current time to compute your OTP.
Server-Side Validation: When you attempt to log in, you type the generated code into the website. The server retrieves your specific secret key from its database, checks its own clock, and performs the exact same mathematical operation. If the server’s result matches the code you typed, you are granted access.
Because device clocks are rarely synchronized to the exact millisecond, the server incorporates time windows. It usually accepts codes generated in the current 30-second block, as well as the immediately preceding and following blocks.
The Technical Flow
Behind the scenes, this system relies on a cryptographic mechanism known as HMAC. You can think of HMAC as a secure mathematical blender. It takes your secret key and the current time—chopped into 30-second intervals—and mixes them together to create a long, complex string of characters. The system then extracts a small, dynamic slice of that long string and converts it into the simple six-digit number displayed on your screen.

Security Considerations
This approach is highly secure for several reasons. The generated OTPs are never transmitted across a network until you type them, and they expire almost instantly. Furthermore, since the server does not store the final codes, a database breach yields nothing useful to an attacker regarding your current OTP.
However, risks remain. If your phone experiences severe time drift, the codes will fail to synchronize with the server. The most critical vulnerability is the secret key itself. If the QR code is intercepted or malware extracts the secret from your device, an attacker can clone your authenticator and generate valid codes.
Moving Beyond Traditional OTPs
Traditional 2FA systems rely on SMS or email. In those models, the server generates a random number, stores it temporarily, and sends it to you over a network. While user-friendly, this method is vulnerable to SIM-swapping and message interception. Authenticator apps eliminate the network transmission step completely. You trade a slight bit of convenience for a massive upgrade in operational security.
Conclusion
Authenticator apps provide a scalable, elegant solution to identity verification. By combining cryptography with synchronized time, they allow systems to authenticate users without the risk of storing the passwords themselves. As digital threats continue to evolve, understanding and utilizing decentralized verification remains essential for keeping modern accounts secure.